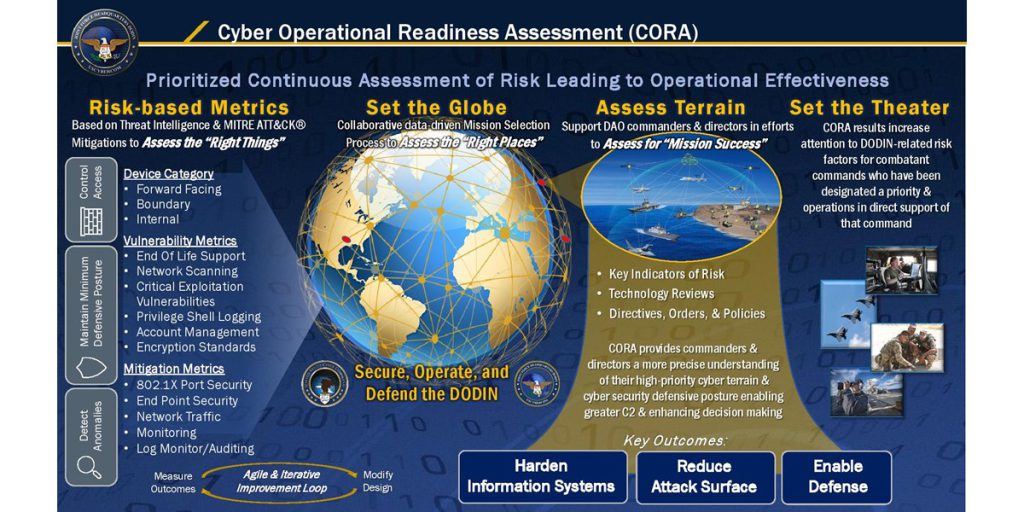
JFHQ-DODIN Officially Launches its New Cyber Operational Readiness Assessment Program
Following a successful nine-month pilot, Joint Force Headquarters — Department of Defense Information Network (JFHQ-DODIN) is officially launching its Cyber Operational Readiness Assessment program. Over the past four years, JFHQ-DODIN has made significant changes to the Defense Department Command Cyber Readiness Inspection program, transforming mindsets from an inspection compliance to an operational readiness underpinning mission…