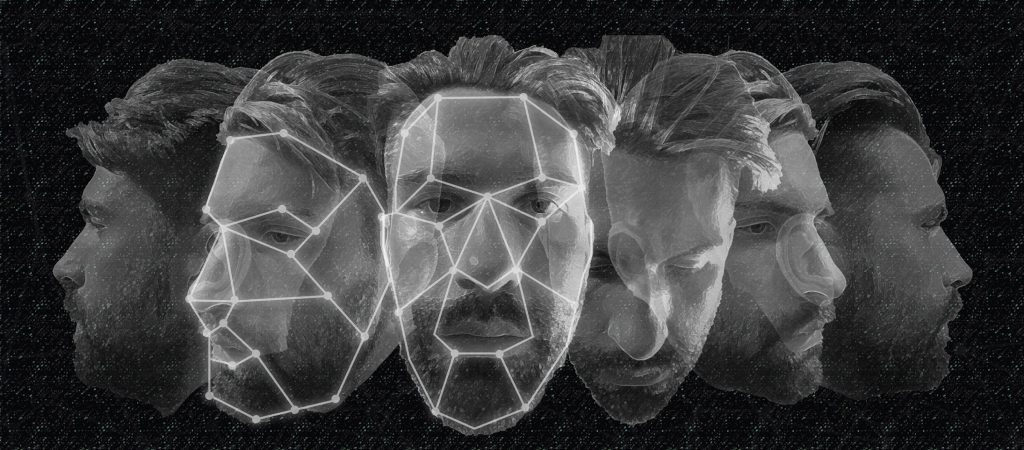
Deepfake Defense Tech Ready for Commercialization, Transition
The threat of manipulated media has steadily increased as automated manipulation technologies become more accessible and social media continues to provide a ripe environment for viral content sharing. The speed, scale, and breadth at which massive disinformation campaigns can unfold require computational defenses and automated algorithms to help humans discern what content is real and…