Are you interested in delivering a webinar presentation on your DoD research and engineering efforts?
CSIAC hosts live online technical presentations featuring a DoD research and engineering topic within our technical focus areas.
Host a Webinar with CSIAC
Upcoming Webinars
Improving Security, Privacy, and Authentication With a Quantum-Enhanced TCP/IP Protocol
Secure communications need to exchange encryption keys over encrypted channels often implemented with asymmetric algorithms. Because both the session key transmission and digital signatures use algorithms like RSA (Rivest–Shamir–Adleman), they are vulnerable to future quantum…
Research Challenges for Large Pretrained Models
This webinar will highlight research challenges cutting across U.S. Army, Navy, and Air Force use cases for large pretrained models to include research on the following: multimodal models knowledge distillation for deployment at the edge…
Do I Need Cybersecurity Maturity Model Certification (CMMC) and Why?
On November 2010, President Obama issued Executive Order 13556 that formed the controlled unclassified information (CUI) program. Six years later, the Defense Federal Acquisition Regulation Supplement (DFARS) 252.204-7012 was published, establishing requirements for CUI, making…
Past Webinars
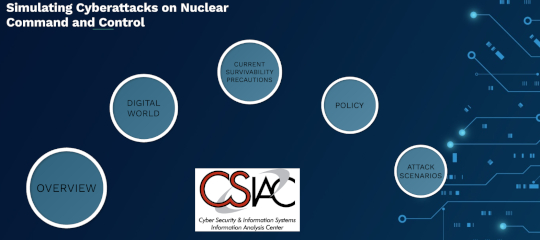
Simulating Cyberattacks on Nuclear Command and Control
During the height of the Cold War, the biggest fear involved the possibility of mutually assured destruction (MAD) from nuclear warfare. However, in today’s digital…
Cybersecurity Simplified
To many, cybersecurity is a well-known but poorly understood topic. System owners specializing in non-software/Information Technology (IT) functions have undoubtedly been warned of the potentially…
Highly Secured Blockchain Technology for Strategic Supply Chain Management
The blockchain technology is a game changer to enhance the security of our supply chain, and smart manufacturing. The technology enables the tracking and recording…
Bug Bounty Adoption “Crowdsourced Security”
In an effort to strengthen the cyber defense and cyber resilience measures within information technology systems, government and industry partners are increasingly turning to ethical…
Cybersecurity Supply Chain Risk Management (C-SCRM)
Supply chain attacks, also referred to as value-chain or third-party attacks, occur when hackers are able to infiltrate a system using loopholes in third-party logistics…
Publishing Domain Specific Source Code for Reuse and Maintenance
Software reuse of components supplied by language libraries and libraries affiliated with languages are great success stories. However, reuse of domain specific code – that…