Are you interested in delivering a webinar presentation on your DoD research and engineering efforts?
CSIAC hosts live online technical presentations featuring a DoD research and engineering topic within our technical focus areas.
Host a Webinar with CSIAC
Upcoming Webinars
Research Challenges for Large Pretrained Models
This webinar will highlight research challenges cutting across U.S. Army, Navy, and Air Force use cases for large pretrained models to include research on the following: multimodal models knowledge distillation for deployment at the edge…
Do I Need Cybersecurity Maturity Model Certification (CMMC) and Why?
On November 2010, President Obama issued Executive Order 13556 that formed the controlled unclassified information (CUI) program. Six years later, the Defense Federal Acquisition Regulation Supplement (DFARS) 252.204-7012 was published, establishing requirements for CUI, making…
Past Webinars
Encryption Awareness
Learn the basics about what encryption is and how it works. This short video describes symmetric and asymmetric encryption. This is part 1 of a…
eMASS, the True Story
This webinar covers the realities of the Enterprise Mission Assurance Support Service (eMASS): what works well, what does not work, and how to best make…
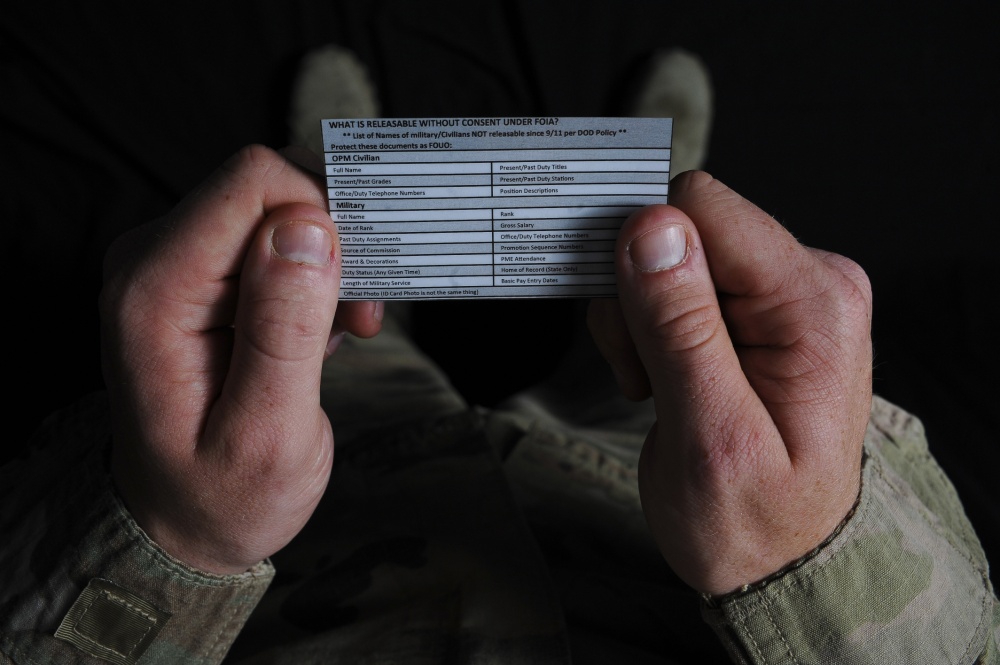
Personally Identifiable Information (PII) – What is it?
Learn about Personally Identifiable Information (PII).
Democratize Anomaly Detection Technologies: Challenges, Advances, and Opportunities
The mature signature-based intrusion detection technology has been the first line of defense in the cyberspace. However, due to the perpetual cat-and-mouse game and asymmetry…